- Prerequisites: Have your AWS credentials ready, including access key and secret access key, with permissions to access the EKS role.
- Configuring Playbooks: In the Playbooks dashboard, navigate to Integrations > AWS EKS. Enter your AWS access key ID, secret access key, region, EKS role ARN, and External ID (you generate this in Step 2 below and add it when creating the role in the AWS console).
- Testing the Integration: Test the integration.
Steps to create a new user:
Step 1: Create a policy (AmazonEKSViewNodesAndWorkloadsPolicy) with this json:
Step 2: Generate External ID and create the role (eks-reader)
- In DrDroid, go to Integrations → AWS EKS. In the External ID field click Generate, then copy the value (you will use it in the AWS console and again when saving the connector).
- In the AWS console, go to IAM → Roles → Create role. Attach the policy from Step 1 (AmazonEKSViewNodesAndWorkloadsPolicy).
- For Trust policy, choose Custom trust policy and use the following (replace
<YOUR_ACCOUNT_ID>with your AWS account ID and<EXTERNAL_ID_FROM_DRDROID>with the value you generated in step 1):
- Name the role (e.g.
eks-reader) and create it. You will enter this role’s ARN and the same External ID in DrDroid when configuring the connector.
Step 3: Create a policy (AmazonEKSAssumeEKSReaderPolicy) in your IAM that allows assuming this role with the following json:
Step 4: Create a new user in your IAM with both policies attached
Attach AmazonEKSAssumeEKSReaderPolicy and AmazonEKSViewNodesAndWorkloadsPolicy to the user. You don’t need to add any group to the user.Step 5: Create an access key
Once the user is created, go to Security credentials and create an access key.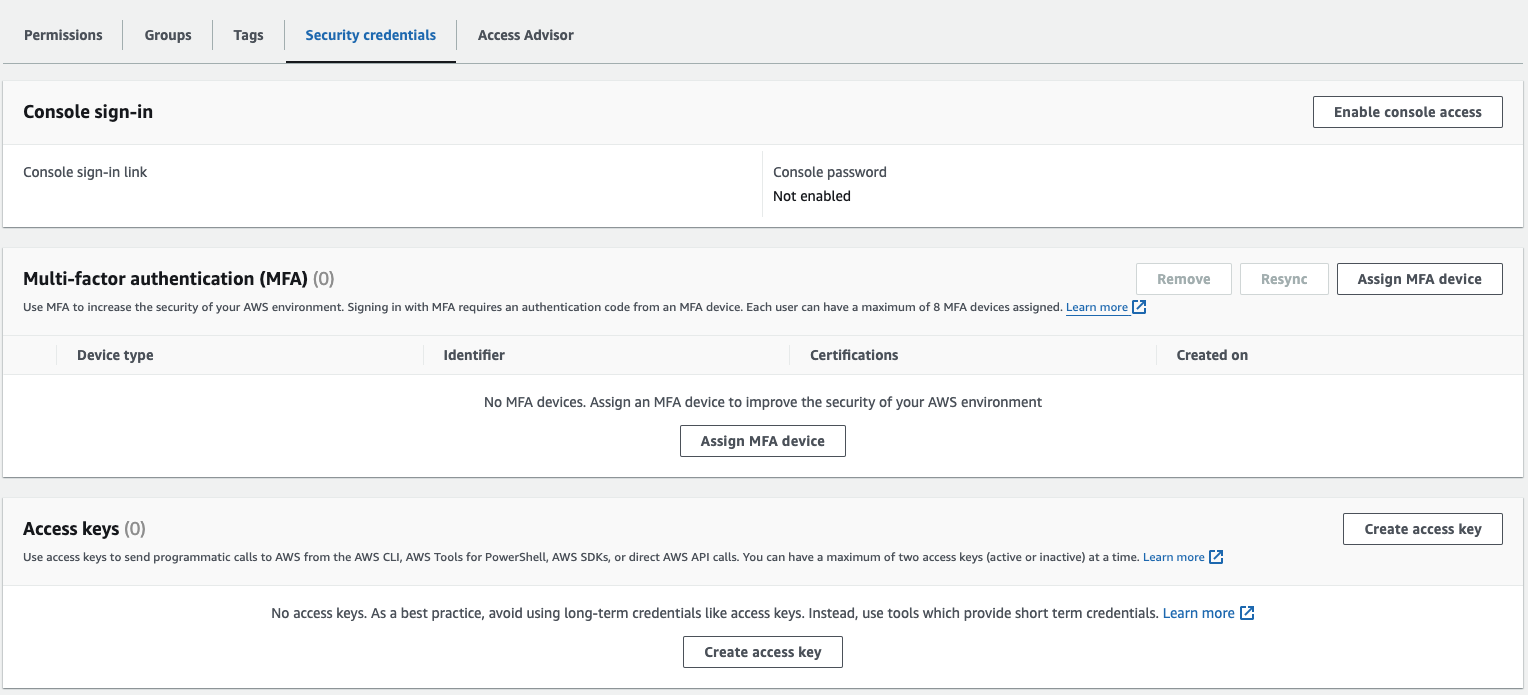
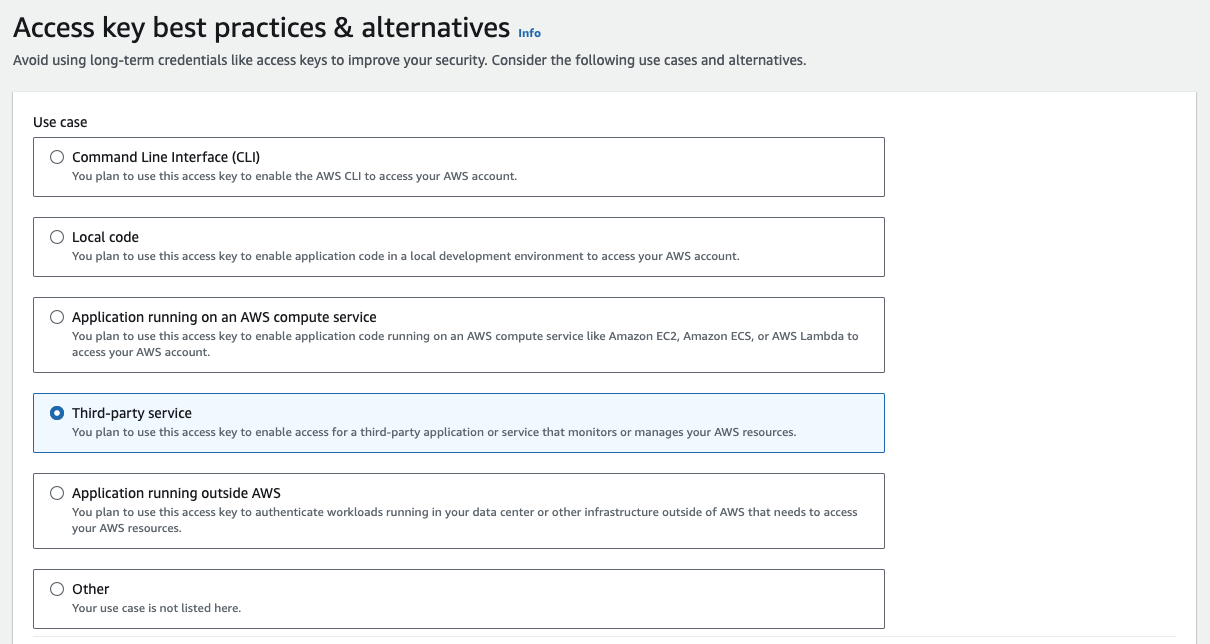
Step 6: Select “Third-party service” while creating the key
Step 7: Add credentials and External ID in DrDroid
Copy the access key and secret key into Integrations → AWS EKS on the Integrations page. Enter the Assumed Role ARN (the eks-reader role ARN), AWS Region, and the same External ID you generated in Step 2. Test the integration, then save.Step 8: Give the eks-reader role permission to query the cluster We’ll do that by creating a config map, a cluster role and a new role binding.
- kubectl apply -f auth.yaml -n kube-system
- kubectl apply -f role.yaml -n kube-system

